Mumble con Tails

En un mundo digitalizado, las llamadas por internet se han convertido en una alternativa utilizada por millones de personas para comunicarse de manera global a bajo costo.
- Introducción
- Terminología
- Nota de descargo
- Descripción del problema
- Desarrollo de solución propuesta
- Manos a la obra
- Conclusiones
- Código fuente
Introducción
En un mundo digitalizado, las llamadas por internet se han convertido en una alternativa utilizada por millones de personas para comunicarse de manera global a bajo costo. Si bien los beneficios de esta tecnología son evidentes, las implicaciones relacionadas con la privacidad son desconocidas por la mayoría de los usuarios. Por esto valdría preguntarse si alguien puede monitorear, grabar o escuchar estas llamadas.
En la primera sección de este artículo se explicará el modelo de amenaza y la solución propuesta para el mismo. A través de imágenes, se esquematizará el modelo de comunicación tradicional versus uno autónomo. En la segunda sección del artículo se explicará de manera práctica el uso de la solución propuesta. Finalmente, se presentan conclusiones y recomendaciones.
Terminología
Mumble : Sistema cliente-servidor que permite establecer comunicaciones de audio entre dos o más personas a través de la Internet.
Tails: Sistema operativo live orientado a preservar la privacidad y anonimato basado en Linux y Tor. En caso de no saber cómo instalarlo se recomienda seguir la documentación oficial.
Tor: Tor es una red distribuida que permite tener anonimato en Internet. Es comúnmente utilizado mediante un navegador que permite acceder a sitios web de forma anónima. Adicionalmente Tor permite exponer servicios TCP accesibles solo dentro de su red conocidos como Servicios Ocultos o Servicios Cebolla.
VoIP: Las comunicaciones de Voz sobre IP (VoIP por sus siglas en inglés) permiten establecer llamadas de voz a través de redes de datos. Su uso más común es para comunicarse a través de la Internet.
Nota de descargo
El siguiente artículo es una propuesta conceptual que no ha sido suficientemente probada por lo cual se recomienda utilizarla bajo su propia responsabilidad.
Descripción del problema
Servicios de telefonía IP como Skype, Hangouts, WhatsApp y otros permiten comunicarse de forma rápida y barata a nivel global. Si bien los beneficios de los mismos son evidentes, también existen implicaciones relacionadas con la privacidad. Las aplicaciones antes mencionados centralizan las comunicaciones de cientos de millones de personas. Por ejemplo, Microsoft en el caso de Skype, o Google en el de Hangouts tienen acceso total a todas las comunicaciones que atraviesan sus servidores, como se pueden ver en la Imagen 1. ‘
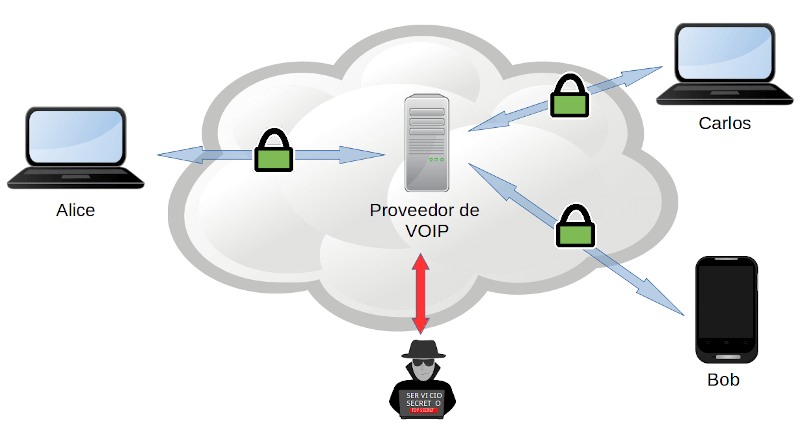
Imagen 1: Esquema de VOIP tradicional.
Por este motivo, si la comunicación no está cifrada entre extremo, estas empresas pueden espiar las llamadas de sus usuarios. Si las mismas estuvieran cifradas, los proveedores no podrían escuchar las comunicaciones pero tendrían acceso a los metadatos de las mismas. Esto les permitiría saber quién se comunica con quién, cuánto tiempo dura la llamada, que miembros intervienen, su geolocalización, su dirección IP, etcétera.
La solución propuesta en este artículo busca que dos o más personas puedan comunicarse evitando los riesgos expuestos anterioremente, por ejemplo, que la comunicación se realice sin que nadie más sepa que la misma existió. Para alcanzar este objetivo se utilizará el sistema Mumble en combinación con Tails.
Tails es un sistema operativo basado en Linux y Tor que, entre otras cosas, permite tener mensajería instantánea y correo cifrado. Estas tecnologías combinadas permiten ocultar los datos y metadatos de las comunicaciones; sin embargo, Tails no provee la capacidad de tener comunicaciones secretas de voz. A diferencia de los mensajes de texto o correos electrónicos, las comunicaciones de voz suelen funcionar mediante el protocolo UDP que no es compatible con Tor.
Mumble es un sistema de audio conferencia utilizado como complemento para videojuegos en línea y para realizar reuniones a través de la Internet. Tiene la característica de utilizar poco ancho de banda y funcionar bien con conexiones de baja latencia. Además Mumble, a diferencia de otras soluciones de VoIP, es compatible con el protocolo TCP, por lo que puede funcionar con Tor.
Desarrollo de solución propuesta
Se desarrollaron scripts de bash que permiten automatizar la instalación de Mumble en Tails, tanto en modo persistente como en **amnesia **. Estos scripts además configuran el servicio oculto de Tor. El nombre del servicio oculto sirve como la dirección a la cual se tendrán que conectar los participantes de la conversación. Como uno de los participantes ejecutará el servidor de Mumble, nadie por fuera de la conversación sabrá que la comunicación se dio, como se puede ver en la Imagen 2.
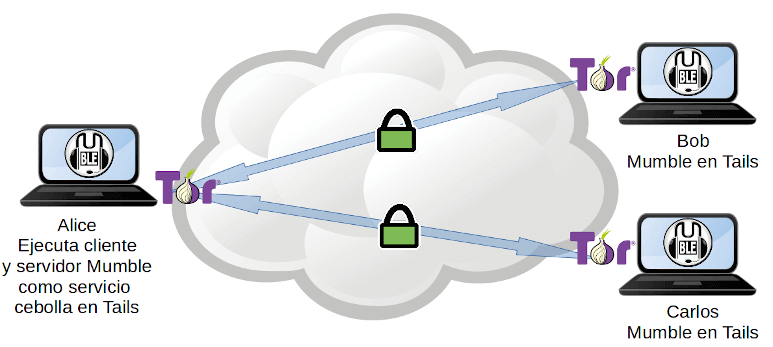
Imagen 2: Solución Mumble con Tails.
Descripción de los Scripts:
setup-mumble.sh
- Actualiza el reposiorio de apt.
- Instala el servidor y el cliente Mumble.
- Configura el servicio oculto de Tor.
- Muestra en pantalla la dirección del servicio oculto y la copia al porta papeles.
Para modo de persistencia, copiar las configuraciones del servidor Mumble y del servicio oculto a la unidad de persistencia.
purge-mumble.sh
- Remueve la configuración de Mumble y del servicio oculto.
- Elimina los paquetes mumble-server y mumble, así como las dependencias que ya no son necesarias.
restore-mumble.sh
- Para ser utilizado solo en modo persistencia.
- Copia las configuraciones del servidor Mumble y del servicio oculto desde el volumen de persistencia a la ubicación correspondiente en el sistema operativo.
- Reinicia Tor para exponer el servidor Mumble a través del servicio oculto.
- Muestra en pantalla la dirección del servicio oculto y la copia al porta papeles.
Manos a la obra
Iniciar el sistema operativo Tails y en la pantalla de bienvenida establecer una clave de usuario root.
Imagen 3: Pantalla de bienvenida de Tails
Asegurarse de copiar los scripts en un lugar accesible como /home/amnesia/mumble-scripts.
Para modo de persistencia, se recomienda copiar los scripts en /home/amnesia/Persistent/mumble-scripts para que sean accesibles después del reinicio del sistema.
Abrir la consola.
Cambiar al usuario root a través del comando sudo.
sudo -iDar permisos de ejecución a los scripts mediante el comando:
chmod 755 /home/amnesia/mumble-scripts/*.shPara configurar el servidor Mumble ejecutar
/home/amnesia/mumble-scripts/setup-mumble.shAl terminar la ejecución del comando se mostrará en pantalla la dirección “.onion” como se puede ver en el recuadro rojo de la siguiente imagen. De manera alternativa, la dirección se copia automáticamente en el portapapeles, lo que permite compartir de forma simple la dirección.
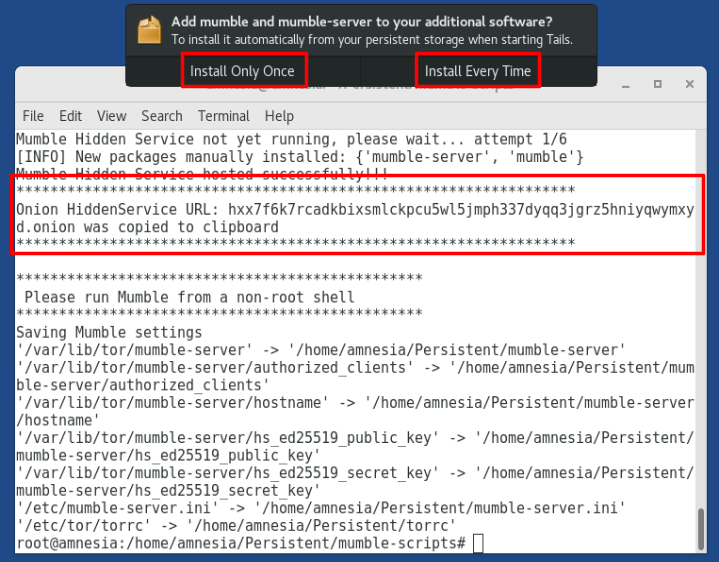
Imagen 4: Script setup-mumble.sh en ejecución.
Es importante notar que en la imagen que se presenta la opción de “Install Only Once” e “Install Every Time”. La primera opción se debe seleccionar en caso de que se vaya a utilizar Mumble por una única vez; la segunda opción se recomienda cuando se vaya a utilizar Mumble de forma recurrente y se quiere tenerlo siempre disponible.
En el menú Applications, dentro de la sección Internet aparecerá el programa Mumble, como se puede ver en la siguiente imagen:
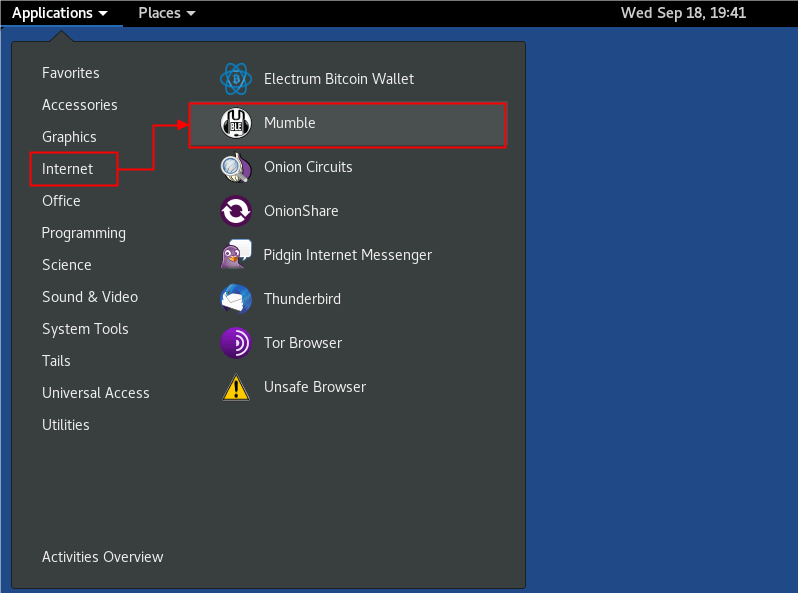
Imagen 5: Ejecución de Mumble.
Nota: De manera alternativa se puede ejecutar el comando mumble desde una terminal sin privilegios.
Compartir la dirección .onion con las personas que participarán en la comunicación, para esto se pueden utilizar las herramientas provistas por Tails como chat cifrado, correo cifrado u otras formas.
Configurar Mumble
La primera vez que se ejecuta Mumble se iniciará un asistente de configuración. En caso de no tener audífonos es recomendable en la ventana de “Voice Activiy Detection” seleccionar la opción “push to talk”. De esta manera se puede utilizar el ratón o una tecla para prender el micrófono solamente cuando se va a hablar y evitar problemas de eco.
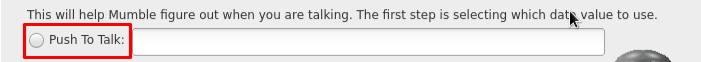
Imagen 6: Establecer opción push to talk en Mumble
Una vez terminado el asistente de audio se debe crear una nueva conexión e ingresar a la misma. Para esto se debe seleccionar la opción “add-new” (1).
En la configuración de la conexión se debe ingresar la información requerida:
- Label: Nombre de la conexión.
- Address: La dirección .onion.
- Port: Dejar la configuración por defecto.
- Username: Poner un nombre de usuario cualquiera.
En el paso 3 se debe seleccionar la conexión creada y poner “connect”. Luego se presentará un error de certificado, es seguro ignorarlo ya que la autenticación se la hace a través del servicio oculto de Tor.
Imagen 7: Configuración y conexión al servidor Mumble.
Una vez realizados estos pasos, tanto Bob como Alice podrán tener comunicación de Voz/IP en Tails.
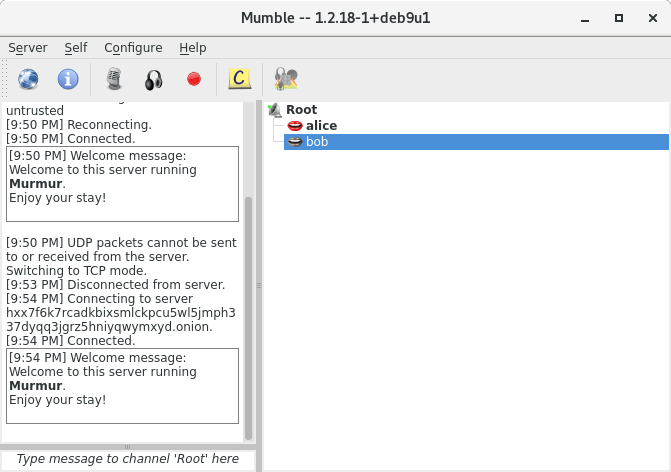
Imagen 8: Conexión establecida y clientes conectados
Conclusiones
Esta solución aprovecha las características de seguridad, privacidad y anonimato que Tails provee y las combina con Mumble para ofrecer una comunicación aceptablemente segura. Si el proveedor local de Internet intenta espiar la comunicación, este podrá saber que Alice esta utilizando Tor pero no para qué. Al no existir un proveedor de VoIP, las comunicaciones son autónomas y se elimina esteposible adversario del modelo de amenaza.
No es una solución perfecta por lo que hay que tomar ciertas consideraciones. El uso de Tor hace que la transmisión de voz tenga un retraso por lo que la conversación puede ser sobrepuesta. En este caso es particularmente importante que una persona hable a la vez.
Es importante considerar el ancho de banda de subida de las conexiones locales ya que la comunicación es en dos vías (full-duplex). Este detalle es primordial para la persona que ejecuta el servidor Mumble ya que tendrá que abrir n canales de comunicación. Es decir que si Alice gestiona una conferencia de 4 personas tendrá que abrir 4 canales de comunicación.
Al ser una prueba de concepto, es necesario tener conocimientos básicos de línea de comando en Linux. Para una futura versión sería conveniente empaquetar la solución y de esta manera mejorar la experiencia de usuario.
El sistema operativo Tails ofrece comunicaciones seguras a nivel de chat y correo electrónico, no así las de voz sobre IP en tiempo real. Los scripts desarrollados pueden servir como un insumo para que el proyecto Tails lo considere en versiones futuras.
Código fuente
En esta sección se muestra el código fuente de los scripts desarrollados para la solución.
setup-mumble.sh
volver
#!/bin/bash
TORRC_ROOT=/etc/tor
ETC_ROOT=/etc
HSDIR_ROOT=/var/lib/tor
PERSISTENT_DEVICE=/dev/mapper/TailsData_unlocked
PERSISTENT_ROOT=/home/amnesia/Persistent
# Hidden Service port
HS_PORT=64738
MUMBLE_SERVER_STATUS=-1
TOR_STATUS=-1
ONION_URL='-'
## Validating Tor service status
TOR_STATUS=$(systemctl is-active tor)
echo "Tor service status ${TOR_STATUS}"
if [ "${TOR_STATUS}" == "inactive" ];
then
echo "Starting Tor service"
systemctl start tor
sleep 5
fi
## Install Mumble Client and Server
apt-get update
apt-get install mumble-server mumble -y
## Configure Hidden Service script for Mumble
echo "Backing up original torrc configuration"
cp -pv ${TORRC_ROOT}/torrc ${TORRC_ROOT}/torrc.orig
echo "Configure Hidden Service for Mumble in torrc"
sed -e "/#HiddenServicePort 22 127.0.0.1:22/a \
\\\\n\
# Mumble hidden service configuration.\n\
HiddenServiceDir ${HSDIR_ROOT}/mumble-server/\n\
HiddenServicePort ${HS_PORT} 127.0.0.1:${HS_PORT}" \
< ${TORRC_ROOT}/torrc.orig \
> ${TORRC_ROOT}/torrc
## Configure Mumble Server script to listen only on localhost
echo "Backing up original Mumble Server configuration"
cp -pv ${ETC_ROOT}/mumble-server.ini ${ETC_ROOT}/mumble-server.ini.orig
echo "Configure Mumble Server to bind to localhost"
sed -e "s/#host=/host=localhost/" \
< ${ETC_ROOT}/mumble-server.ini.orig \
> ${ETC_ROOT}/mumble-server.ini
## Validating Mumble server service status
MUMBLE_SERVER_STATUS=$(systemctl is-active mumble-server.service)
echo "Mumble Server status ${MUMBLE_SERVER_STATUS}"
if [ "${MUMBLE_SERVER_STATUS}" == "active" ];
then
echo "Restarting Mumble Server"
systemctl restart mumble-server.service
fi
## Validating Tor service status, make sure it is running.
TOR_STATUS=$(systemctl is-active tor)
echo "Tor service status ${TOR_STATUS}"
if [ "${TOR_STATUS}" == "active" ];
then
echo "Restarting Tor service"
systemctl restart tor
for i in {1..6}
do
if [ -f ${HSDIR_ROOT}/mumble-server/hostname ];
then
echo "Mumble Hidden Service hosted successfully!!!"
break
fi
echo "Mumble Hidden Service not yet running, please wait... attempt ${i}/6"
sleep 5
done
if [ -f ${HSDIR_ROOT}/mumble-server/hostname ];
then
ONION_URL=$(cat ${HSDIR_ROOT}/mumble-server/hostname)
echo ${ONION_URL} | xclip -selection c
echo "******************************************************************"
echo "Onion HiddenService URL: ${ONION_URL} was copied to clipboard"
echo "******************************************************************"
echo
echo "************************************************"
echo " Please run Mumble from a non-root shell"
echo "************************************************"
else
echo "************************************************"
echo "Mumble Hidden Service hosting failed!!!"
echo "Please check the system and try again..."
echo "************************************************"
fi
fi
## Save data for persistent mode.
if [ -e ${PERSISTENT_DEVICE} ]
then
echo "Saving Mumble settings"
cp -avr ${HSDIR_ROOT}/mumble-server ${PERSISTENT_ROOT}
cp -pv ${ETC_ROOT}/mumble-server.ini ${PERSISTENT_ROOT}
cp -pv ${TORRC_ROOT}/torrc ${PERSISTENT_ROOT}
firestore-mumble.sh
volver
#!/bin/bash
TORRC_ROOT=/etc/tor
ETC_ROOT=/etc
HSDIR_ROOT=/var/lib/tor
PERSISTENT_ROOT=/home/amnesia/Persistent
ONION_URL='-'
# Move folder and files needes from Persistent location to respective
# OS locations for order to host Mumble hidden service.
cp -avr ${PERSISTENT_ROOT} ${HSDIR_ROOT}
cp -pv ${PERSISTENT_ROOT}/mumble-server.ini ${ETC_ROOT}
cp -pv ${PERSISTENT_ROOT}/torrc ${TORRC_ROOT}
## Restart Tor service to initialize Mumble hidden service
echo "Restarting Tor service"
systemctl restart tor
for i in {1..6}
do
if [ -f ${HSDIR_ROOT}/mumble-server/hostname ];
then
echo "Mumble Hidden Service hosted successfully!!!"
break
fi
echo "Mumble Hidden Service not yet running, please wait... attempt ${i}/6"
sleep 5
done
## Get the Mumble Hidden Service URL and display it to the user
if [ -f ${HSDIR_ROOT}/mumble-server/hostname ];
then
ONION_URL=$(cat ${HSDIR_ROOT}/mumble-server/hostname)
echo ${ONION_URL} | xclip -selection c
echo "******************************************************************"
echo "Onion HiddenService URL: ${ONION_URL} was copied to clipboard"
echo "******************************************************************"
echo
echo "************************************************"
echo " Please run Mumble from a non-root shell"
echo "************************************************"
else
echo "************************************************"
echo "Mumble Hidden Service hosting failed!!!"
echo "Please check the system and try again..."
echo "************************************************"
fipurge-mumble.sh
volver
#!/bin/bash
ETC_ROOT=/etc
TORRC_ROOT=/etc/tor
HSDIR_ROOT=/var/lib/tor
PERSISTENT_DEVICE=/dev/mapper/TailsData_unlocked
PERSISTENT_ROOT=/home/amnesia/Persistent
# Starting the purge
echo "Stopping Mumble Server"
systemctl stop mumble-server.service
echo "Purging mumble"
apt purge mumble mumble-server -y
apt autoremove -y
echo "Restoring torrc"
cp -pv ${TORRC_ROOT}/torrc.orig ${TORRC_ROOT}/torrc
echo "Removing Mumble hosting file"
rm -r ${HSDIR_ROOT}/mumble-server
echo "Restarting Tor service"
systemctl restart tor
# Purge data for persistent mode.
if [ -e ${PERSISTENT_DEVICE} ]
then
echo "Purging persistent data for Mumble"
rm -f ${ETC_ROOT}/mumble-server.ini.orig
rm -f ${PERSISTENT_ROOT}/mumble-server.ini
rm -rf ${PERSISTENT_ROOT}/mumble-server
fi