Segundo Factor de Autenticación
En el artículo anterior, se revisaron algunos conceptos importantes alrededor del manejo de contraseñas y cómo generarlas de manera más segura.
En el artículo anterior, se revisaron algunos conceptos importantes alrededor del manejo de contraseñas y cómo generarlas de manera más segura. Esto constituye la primera puerta de seguridad en un sistema. Suponiendo que se tiene una llave por cada puerta en un edificio, cada una se usa en su puerta correspondiente y esta se abre sin dificultad. Pero, si una tercera persona logra hacerse de una de las llaves o hacer una copia, conociendo qué puerta abrir con dicha llave, queda comprometida la seguridad de la puerta y así, de todo el edificio.
Cuando se usa una contraseña por cada cuenta que se administra, se logra mejorar la seguridad, pero esto sigue siendo insuficiente para casos en los que las contraseñas quedan comprometidas por una de las tantas causas de fuga o robo de datos. Los usuarios, frecuentemente son víctimas de ataques de «suplantación de identidad» o phishing, siendo este tipo de delito uno de las más comunes y una forma efectiva que permite a terceros con malas intenciones o criminales, hacerse de información privada o confidencial de una forma fraudulenta, usando correos electrónicos u otro tipo de comunicación electrónica, mensajes e incluso, llamadas telefónicas. Uno de los casos más comunes es cuando se recibe un correo electrónico, aparentemente genuino, con un enlace a una página de inicio de sesión similar a la de Facebook, Google, Instagram u otros, en la que insertando la información de usuario y contraseña, el atacante captura la información proporcionada, lo que le permitiría el acceso a cualquiera de los sitios web mencionados anteriormente.
Sin embargo, usando el mismo ejemplo mencionado arriba, la situación mejora si el atacante con una llave, al abrir la puerta, se encuentra con otra que requiere una llave diferente a la que usó en la primera. Esto, entre otros nombres, se conoce como verificación en dos pasos.
Verificación en dos pasos
Del Inglés Two-Factor Authentication (2FA), la verificación en dos pasos, segundo factor de autenticación o autenticación de dos factores, es un método para confirmar que un usuario es quien dice ser, combinando 2 o más de los siguientes factores:
- Algo que el usuario conoce (Ej. una contraseña, la respuesta a una pregunta)
- Algo que el usuario posee (Ej. un teléfono, una tarjeta de coordenadas)
- Una característica física (Ej. datos biométricos, voz, huellas dactilares)
Un ejemplo real de este tipo de verificación, es cuando se retira dinero de un cajero automático. El cajero solicita insertar la tarjeta de débito o crédito (algo que se posee) y un código secreto conocido como PIN (algo que se sabe), al usar estos dos componentes, el cajero automático valida la identidad y permite el retiro del dinero solicitado.
Factor de conocimiento
El factor de conocimiento es básicamente aquello que el usuario conoce, por ejemplo un PIN o contraseña. Los niveles de seguridad en este tipo de factor, varía según los sistemas que lo implementan. Algunos por ejemplo, piden un código de 4 dígitos, pero otros usan una respuesta a una pregunta de seguridad, siendo esta última variante una de las más inseguras, debido a que se pueden determinar las respuestas teniendo información sobre la vida de la persona como fecha de nacimiento, nombre de una mascota, cantidad de hijos, etc., y no conlleva demasiado esfuerzo el lograrlo.
Factor de posesión
Este factor involucra un objeto, normalmente entregado por la persona u organización que realiza la verificación de identidad. Algunos bancos por ejemplo, cuando se desea realizar una transferencia o alguna operación que requiera una identificación de la identidad del usuario, solicitan un código aleatorio que generalmente se obtiene usando una tarjeta de coordenadas, que no es más que una matriz de letras (normalmente desde la A a la F) y números (0-9). Para ello, el sistema solicita una combinación que sólo se puede obtener según esa tarjeta.
El factor de posesión o propiedad, combinado con el factor de conocimiento, es uno de los más populares. La fórmula consiste en:
ALGO QUE SE CONOCE + ALGO QUE SE POSEE.
Características físicas del usuario
Las empresas comercializadoras de computadoras y teléfonos usan mucho este tipo de identificación en sus productos, con la intención de hacer más fácil al usuario el desbloquear sus dispositivos. Por ejemplo, hoy se puede desbloquear un teléfono inteligente usando las huellas dactilares, alguna característica biométrica (reconocimiento facial) y la propia voz.
El usar características físicias como un factor de autenticación, aparenta un método más seguro para los usuarios de estos dispositivos, pero conlleva un riesgo su uso, ya que una contraseña o código se puede cambiar siempre, pero no las características físicas. Para desbloquear un dispositivo usando estas características, en contra de la voluntad del propietario, existen múltiples métodos disponibles para hacerlo. En este aspecto, Hollywood ha dado suficientes ideas de cómo lograrlo con películas al estilo James Bond o Misión Imposible.
Contraseñas de un solo uso
Hasta ahora se ha descrito cuáles son los tipos de componentes de una autenticación en dos pasos, pero ¿cuál es el más recomendable? La respuesta a esta interrogante depende del modelo de amenaza que se está enfrentando y cómo pueden ser usadas en correspondencia con cada modelo de amenaza. En este caso, para un usuario común, una buena opción sería el uso de contraseñas que se usan una sola vez. Las contraseñas que se usan una vez u one-time password (OTP), como su nombre lo indica, son contraseñas o tipos de contraseñas que tienen validez para una única sesión. Este tipo de contraseñas, tiene una ventaja superior a las contraseñas tradicionales, como evitar ataques del tipo repetición. Algunos sistemas que usan contraseñas de un solo uso aseguran una implementación de 2FA, al requerir que el usuario tenga acceso a algo que posee (como un teléfono) o algo que la persona conoce.
Entre los tipos de contraseñas de un solo uso, existen dos populares, las HMAC-based One-time Password (HOTP) y las Time-based One-time Password (TOTP). La principal diferencia entre los dos tipos, es que las HOTP generan contraseñas válidas hasta que se usen o se genere un segundo HOTP. En el segundo caso, con TOTP se generan contraseñas de un solo uso válidas por un límite de tiempo, es decir, si se vence el tiempo por el cual la contraseña es válida, entonces dicha contraseña deja de ser válida y por siguiente, es descartada. Algunas empresas populares implementan servicios de 2FA usando los dos servicios HOTP y TOTP.
Las TOTP, aún siendo una extensión de las HOTP, tiene mejoras de seguridad con respecto a estas. Han sido adoptadas como un estándar por la Internet Engineering Task Force. A pesar de que son más seguras, entre otras causas, son vulnerables a ciertos tipos de ataques en los que se pueden capturar las credenciales al igual que las contraseñas tradicionales.
Caso de estudio
Al ser TOTP un método recomendable, en el siguiente ejercicio se realizará la configuración de este factor en un escenario específico. Para ello, se requiere instalar en el teléfono una aplicación de autenticación de dos factores para sistemas que utilizan protocolos de contraseñas de un solo uso. En este caso, se estará usando FreeOTP, una app para Android y iPhone que implementa los estándares HOTP y TOTP.
Habilitando TOTP en GitHub
Una vez completado el inicio de sesión en GitHub:
1. En la esquina superior derecha (barra de navegación), hacer clic en la foto de perfil y luego hacer clic en la opción “Configuración”
2. En la barra lateral de configuración del usuario, haga clic en “Seguridad”
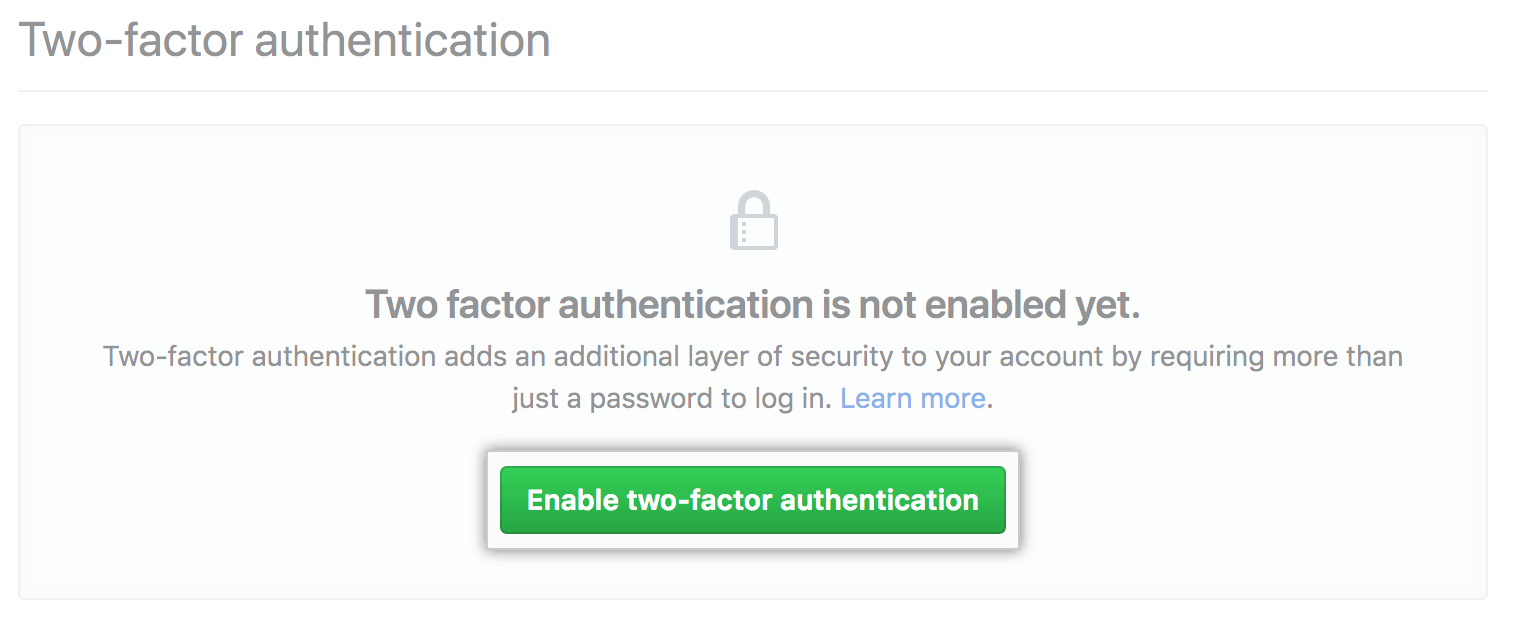
3. En Autenticación de dos factores, haga clic en “Habilitar autenticación de dos factores”
4. En la página de autenticación de dos factores, hacer clic en “Configurar mediante una app”
5. Guardar los códigos de recuperación en un lugar seguro
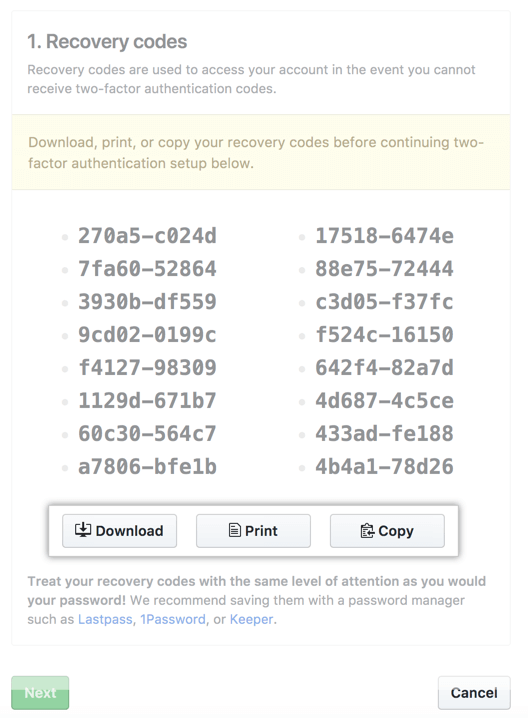
Los códigos de recuperación permiten recuperar el acceso a la cuenta en caso de perder el acceso.
6. Después de guardar los códigos de recuperación de dos factores, hacer clic en “Siguiente”
7. En la página de autenticación de dos factores, realizar una de las siguientes opciones
- Escanear el código QR con la app del dispositivo móvil. Luego de escanear, la app muestra un código de seis dígitos que se debe ingresar en GitHub.
- Si no se puede escanear el código QR, hacer clic en enter “Escribir este código de texto” para ver un código que se pueda copiar e ingresar manualmente en GitHub.
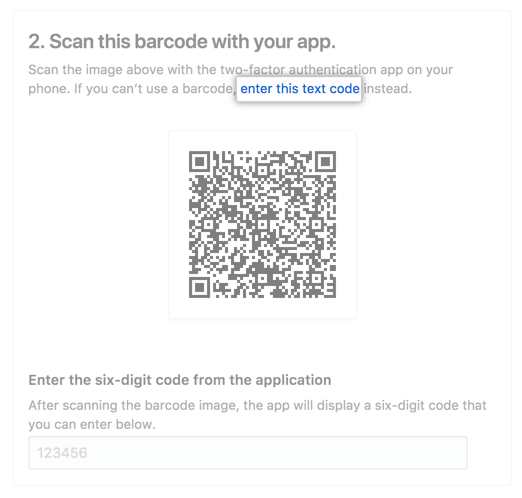
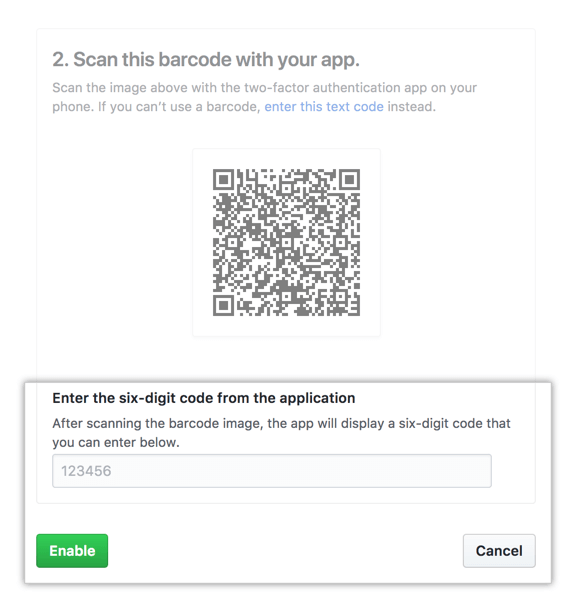
8. La aplicación móvil TOTP guarda la cuenta en GitHub y genera un nuevo código de autenticación cada un tiempo limitado
En GitHub, en la página 2FA, escribir el código y hacer clic en “Habilitar”.
Más información en GitHub
Recursos y herramientas
Aplicaciones TOTP basadas en la nube:
Habilitar 2FA en sitios populares:
Conclusiones
La verificación en dos o múltiples pasos no garantiza la seguridad o integridad de la información de un usuario en un sistema en su totalidad, algunos de ellos no son suficientes, pero la mejoran en gran medida al realizar el proceso más complejo y agrear pasos extras a la confirmación de la identidad del usuario. El uso de gestores de contraseñas ayuda a tener contraseñas seguras y distintas para cada cuenta, pero este método no es suficiente para defenserse del phishing. El uso del doble factor de autenticación es una forma efectiva de defenderse de este tipo de ataques.
Referencias
- https://es.wikipedia.org/wiki/Autenticaci%C3%B3n_de_m%C3%BAltiples_factores
- https://www.welivesecurity.com/la-es/2014/02/19/doble-factor-autenticacion-que-es-porque-lo-necesito/
- https://en.wikipedia.org/wiki/One-time_password
- https://en.wikipedia.org/wiki/HMAC-based_One-time_Password_algorithm
- https://en.wikipedia.org/wiki/Time-based_One-time_Password_algorithm